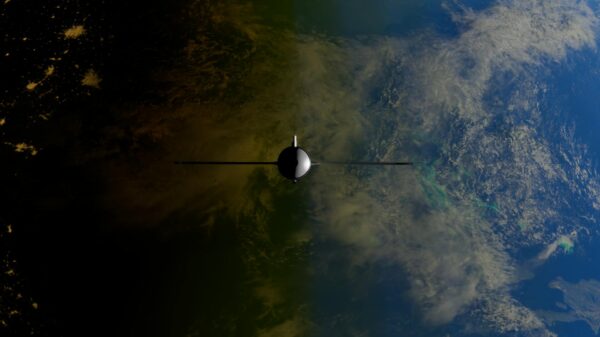
The internet feels invisible. It lives in clouds, it travels through the air, it arrives instantly. But most of the overwhelming majority of global data traffic moves through cables thinner than a garden hose, lying on the seafloor in the dark. And those cables, it turns out, are not as private as the companies running them would have you believe.
Researchers and intelligence analysts have documented for years that submarine fiber-optic cables carry somewhere around 95% of all international internet traffic. Voice calls, financial transactions, military communications, emails, video streams. All of it, compressed into pulses of light, fired through glass threads across ocean beds that span every major continent. The scale alone is staggering: more than 400 active submarine cable systems stretch over a million kilometers combined.
Now, and here’s the part the industry has been reluctant to say plainly, those cables have long been accessible to signals intelligence operations in ways that go well beyond what telecom providers publicly disclose to their customers.
The Access Points Nobody Advertises

The monitoring doesn’t require cutting a cable or physically boarding a ship. The physics of fiber-optic transmission create a natural opportunity: at the landing stations where undersea cables come ashore, data must be converted, amplified, and routed onward. These onshore facilities, located in places like Cornwall in the UK, Long Island in New York, and coastal points across Southeast Asia and the Middle East, are the chokepoints. Control access to those rooms, and you effectively control a lens over a significant portion of global communications.
Intelligence agencies understood this decades before the general public did. What changed around 2013 was that the scope of the access became impossible to quietly manage. Documents revealed at the time showed that some of the world’s most significant intelligence-sharing arrangements, the Five Eyes partnership between the United States, United Kingdom, Canada, Australia, and New Zealand, were partly organized around exactly this kind of cable-tap infrastructure. The cables weren’t just monitored opportunistically. They were treated as a primary collection source.
Telecom companies that owned or co-owned segments of those cables were, in many cases, legally compelled to provide access under national security frameworks. Which sounds like an edge case until you realize those frameworks don’t expire, aren’t publicly disclosed, and don’t require the companies to tell their customers anything at all.
What’s Actually Being Captured

The common assumption is that surveillance of this kind targets specific bad actors. Intercept a terrorist’s phone call, track a money-laundering scheme, follow the digital trail of a weapons program. That’s the justification. The operational reality is considerably broader.
Bulk collection, capturing enormous volumes of data and filtering it afterward, is technically easier than targeted interception at the cable level. The infrastructure doesn’t distinguish between a suspicious financial wire transfer and a grandmother’s video call. It carries everything, and systems downstream sort it. The sorting criteria, in most jurisdictions, are classified.
This is not speculation or conspiracy-adjacent theory. It is documented, litigated, and in some countries, publicly acknowledged by the intelligence agencies themselves. The UK’s GCHQ has been more forthcoming than most intelligence agencies on this topic, with its cable-monitoring activities, conducted under the Tempora program, confirmed through Snowden-era disclosures and subsequent public reporting. In the legislative proceedings, cable interception forms part of its signals intelligence posture. The NSA’s equivalent programs remain far more opaque despite the 2013 disclosures.
What’s less discussed is the commercial dimension. As new cable systems get financed and built, and dozens are currently under construction or recently completed, the question of which governments retain legal access rights to which cables has become a live geopolitical issue. The United States has, in recent years, moved to block or complicate cable projects that would route significant traffic through infrastructure with ties to Chinese state entities. The argument, stated publicly, is about security. The unstated implication is that the monitoring infrastructure already in place is too valuable to allow a rival to replicate.
Why Telecom Companies Stay Quiet

Here’s what’s genuinely strange about this story. The companies involved, the consortia of telecoms, hyperscalers, and national carriers that collectively own and operate the global cable network, are not naive about what’s happening. They operate in the jurisdictions that compel access. Their legal teams have navigated the classified orders. Some have fought them, quietly, in sealed court proceedings. Most have not.
The silence isn’t ignorance. It’s a calculation. Disclosure would trigger customer backlash, regulatory scrutiny, and potentially invalidate the legal shields that protect companies from liability for the access they’ve already granted. So the public posture stays the same: these cables are privately operated, commercially motivated infrastructure. The surveillance angle is treated as a government matter, not a company matter. The gap between those two positions is where most of the interesting truth lives.
There’s also a newer wrinkle. As more hyperscale tech companies, the kind that run global cloud platforms, build or lease their own dedicated cable capacity, the legal landscape gets more complicated. Do the same compelled-access frameworks apply to privately held cable infrastructure that isn’t a licensed telecom carrier? Courts in multiple countries are still working that out.

The internet was designed to route around damage, the old saying goes. What it was never designed to route around was a building full of government equipment at the place where the ocean cable comes ashore.
If 95% of global internet traffic passes through infrastructure that intelligence agencies treat as a collection resource, the question isn’t whether your data has been seen. The question is whether the legal frameworks governing what happens to it afterward are anywhere close to keeping up.
This article was created with AI assistance and reviewed by the author. The review included fact-checking, clarity edits, references and sourcing of images